Advanced Apple Debugging & Reverse Engineering, Chapter 31
Por um escritor misterioso
Last updated 14 março 2025

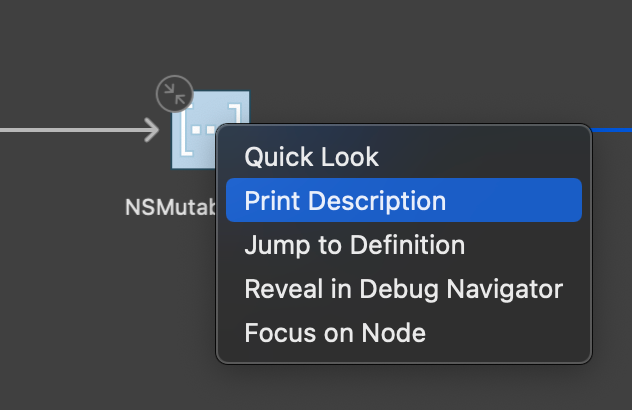
In this chapter, you'll use DTrace to hook objc_msgSend's entry probe and pull out the class name along with the Objective-C selector for that class. By the end of this chapter, you'll have LLDB generating a DTrace script which only generates tracing info for code implemented within the main executable that calls objc_msgSend.

2022-2023 College Catalog by Honolulu Community College - Issuu

Mastering Malware Analysis

Advanced Apple Debugging & Reverse Engineering, Chapter 31: DTrace vs. objc_msgSend

Reverse Engineering Coin Hunt World's Binary Protocol, NCC Group Research Blog

iOS App Reverse Engineering
How to Reverse Engineer an iOS App, by Zafar Ivaev

iOS App Reverse Engineering

Writing Exploits for Win32 Systems from Scratch, NCC Group Research Blog

Advanced Apple Debugging & Reverse Engineering, Chapter 1: Getting Started